Companies are entering new markets based on technology or consumer behavior trends to remain competitive, which requires collaboration with external partners. Johnson & Johnson’s Medical Device unit that saw a quarterly sales increase of 1.3 percent to reach $6.1 billion last year credits the fast-growing success to their innovation model designed to foster collaboration with start-ups and academics.1 As this collaboration increases and information flows more freely, how will companies manage their data security? Does growing collaboration come at a cost of looser security?
More collaboration opens massive risk for organizations’ use of disparate systems and lack of visibility into who has access to knowledge assets. According to a 2015 cybersecurity report by CloudLock, organizations on average collaborate with 865 external parties, yet just 25 of these account for 75 percent of sharing per organization. Unexpectedly, 70 percent of sharing occurs with non-corporate e-mail addresses that security teams have little control over.2 This stresses the importance of managing collaboration in a safer environment.

1. Centralize Data
What can companies do to nurture a safer data environment while staying collaborative? The first step is centralization. It is common for companies to store their data in one place protected by a software vendor to avoid compromised devices, lost data in spreadsheets, or even documents shared via e-mail. Imagine you are managing a large project for a competitive product entering the market, and your design team is communicating with a partner via e-mail. Then, that partner has a security breach, opening access to the project’s sensitive documents. Your project is compromised, or worse, your company receives a tarnished reputation for the next decade. If there is a system in place to access information from a central location, it not only creates easy information sharing but secure management of data with audit trails of who accessed information and when. A central location with information sharing enables collaboration, but permissions must be managed closely.
2. Fortify with Permissions
The second step is controlling who has access to what information. Islands of SharePoint and document sharing sites have little permission management control. CloudLock’s study demonstrates how dangerous document sharing can be when documents become public unintentionally by a simple drag-and-drop action to a public folder; one of the collaborators makes his or her folder public, or a compromised third-party changes the access of their assets.2 Tension builds between whether to lock down provisioning access to outside contributors, which is not collaborative, or establish rigorous standards where users can still give access to their partners but within centrally established boundaries.
A system that enables sophisticated permissions with external partners empowers organizations to ensure who has access to knowledge assets and what level of access is permitted. A multitier approach allows collaboration in real-time within bounds specified by the administrator. Imagine working in a space with an external partner who cannot see your actions, but you are able to gain insights from their quarterly revenue updates, optimizing decision making without physically being in the same room. These tiered permissions are not only more secure but make for highly collaborative environments. Tighter permissions mean little, though, if employees and partners are not informed and frequently updated on best practices in data security.
3. Motivate Compliance
The third step is training employees on compliance and informing them about important regulations in data security. If an employee has sensitive, unencrypted data on his or her laptop that gets compromised, it could not only cost the company millions of dollars but also its competitive advantage. A stolen laptop used by a third-party consultant cost a hospital $1.5 million due to a leak of unencrypted information of thousands of patients that resulted in a federal lawsuit. 3 A central location with permission control could have prevented this mishap.
Therefore, the importance of processes and compliance is crucial to data security. Humans inherently make mistakes, and taking general precautions could save your company by verifying that employees are following security rules and regulations. Are they forwarding copies outside the organization or to personal e-mail? Are employees aware of new security guidelines and precautions, including protections against phishing e-mails? Where are they storing passwords? What is hiding on their local drives? Did they publish nonpublic information to the web without knowing it?
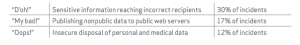
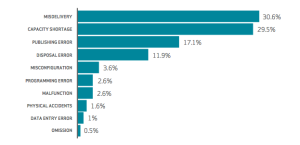
For example, the 2015 Verizon Data Breach Investigations report stated that 60 percent of incidents representing a significant volume of breaches were attributed to errors made by system administrators responsible for incidents such as the following4:
Secure Your Open Innovation Efforts
Information flows more freely as collaboration is encouraged at innovative companies across the globe. It should be no surprise that this opens a considerable risk of sharing data unintentionally. It is important for companies to centralize their data, leverage a system with sophisticated permissions, and train compliance. It should no longer be acceptable to carelessly share sensitive documents and important information unless it is secure and in one place. Letting documents languish on laptops in various locations is risky and less efficient. As collaboration continues to grow, companies will need to adopt systems to simultaneously optimize security and collaboration.
Sources
- “J&J Device Heads Say the New Med Tech Innovation Model Calls for More External Partnerships,” FierceMedicalDevices, October 26, 2015.
- The 1% Who Can Take down Your Organization Q3 2015 Cloud Cybersecurity Report, 2015.
- "North Memorial Health Care Paying $1.5 Million in Federal Privacy Settlement." Star Tribune. N.p., 17 Mar. 2016. Web.
- “2015 Data Breach Investigations Report,” Verizon Enterprise Solutions, 2015.
